Internet Research Project
by Aidan Lim
Privacy Risks in Data Collection and Storage
As the amount of online activities have increased, the amount of sensitive information being leaked has also increased with it.
These include the individual’s personal information,online behavior, and locations. This information is mostly collected by businesses
that will use this information to match the individual’s interests to grab their attention or sell the consumer data to other businesses.
The most common way that these types of information is being taken into is when people go through shopping websites and interact with the
products that they are presented with. This allows them to get a better understanding of the user with every interaction and try to figure
out what they are interested in. The concerning issue with this is that the majority of the people that utilize the internet are not aware
of how their data is being collected and used against them. This leaves them very vulnerable to their data being taken to which can be taken
advantage of. These data are spread very quickly and it is easy to see in everyday life. For example, a user would interact with dog videos
on one platform. After a couple hours, they will begin to see dogs mentioned in different social media platforms even though the user has
never mentioned dogs on these platforms.
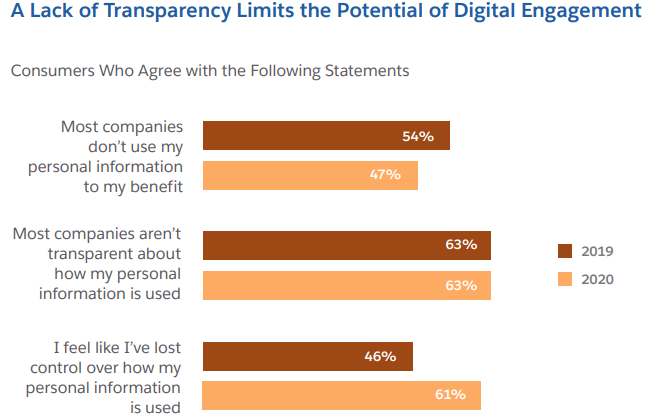
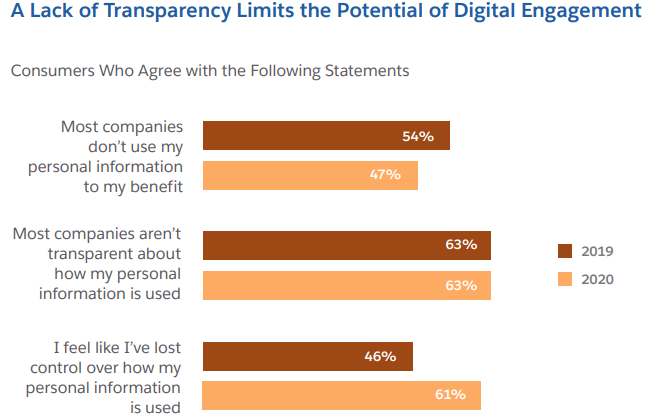
Lack of transparency and informed consent are one of the major problems with the collection of data. Transparency is when users are
aware of how their data is being collected, used or shared. In the current day there are too many companies that use general or complex
language to explain what their right is. This makes it extremely difficult to know exactly what is going on which can lead to hidden data
sharing practice which is how third parties are able to receive this information. Also it is difficult for the user to get out of these
challenges since the systems that they mainly use are too complex for a regular person to comprehend so they are unable to delete or remove
the data that they have on them. Some way to counteract this is by researching companies or businesses that are very open about their data
practices and have a long history of being reliable with the data they collect. This allows people to be able to look through the internet
without fear of their personal data being collected.
Data Breach is another risk that is involved with data collection and storage. It is when sensitive data is stolen without permission.
This is something that occurs more in the present day since everything is now being digitized. This means that all the crucial information
that people need to survive is all now online. Some common ways that a data breach occurs is by cyberattacks. These can occur at any time on
the internet since there are many advertisements that can lead to malware. For example, when going on unprotected websites, there are many popups
that show up whenever they interact with the webpage which can allow them to download something on the user’s device. This can allow them to take
the information within the device which might crucial information like passwords to certain platforms. These problems can lead to financial loss
as they manage to take in bank information and start making charges. They can also steal someone’s identity since they are able to get name, location,
banking information, and more which can be used to commit fraud and causing the user to be blamed. This can be life changing for the worst. One way to
prevent this is to have multi factor authentication or minimizing their activity on the internet.
Misuse and Protection of Computing Resources

Some common ways that computing resources can be misused are unauthorized access and resource exploitation. Downloading unknown software
can lead to trouble and give authorization to people without the user’s awareness. After a user’s information gets leaked it leaves them
very vulnerable to hackers as these attacks can occur at any time. Once they get into one platform with the user’s personal information,
it will allow them to access other platforms and take advantage of it by taking their identity and financial information. The rise of dependency
on technology has made this issue more critical. For example, as people rely on the internet for entertainment, they do not want to pay to watch
a movie/show which leads them towards pirated websites. These are full of malwares and could lead to unapproved installations which would not
only cause their device to not function properly, but can lead to data leaks. Another way that these problems can occur is with the negligence
of the information. Without constantly checking on the user’s information to make sure that is not leaked can leave them too relaxed and unprepared.
It is important to be taking actions such as secure system updates or updating passwords to make sure that these systems are not vulnerable to attacks.
One way to prevent these systems from being exploited is to enforce data protection. With one of these being the ability of backing up
critical data to the cloud to make sure that this information is safe from attacks. If someone were to corrupt or change information it
would be difficult to get it back to normal, but if all the crucial data were to be backed up it would allow them to recover much more
quickly and efficiently. They can also sort their data on how important certain data is. The user should be able to decide which information
should be kept prioritized in protection compared to other information. These can be separated into their own email or password sections and
be used only when needed so the chances of it being attacked is much lower than information that is used daily. It is important to keep monitoring
any data transfers by using tools that can alert the user any time these types of activities are taking place. This will allow them to be aware the
moment anything happens and take action to counter the intrusion.

Another way to prevent systems from being exploited is to implement strong access controls and connection security. Functions such as multi-factor
authentication are very important as it requires more verification and authentication to access some information. These can discourage malicious attacks
as they find it too much effort to attack. For example, gmail requires a two factor authentication by making the user check their cellular device and
manually confirm that they are in fact the person accessing the account. It is also important to access resources using a secure wifi connection. Wifi
connections that are public means that it is unprotected and could leave the device vulnerable to attacks since the encryptions are very weak. A private
wifi connection uses a strong encryption allowing the user to be alone and be able to connect with their resources without the disruption of someone else.
Also it is important to emphasize that end to end encryption resources since it means that these data transfers that are occurring are protected, and prevents
others from accessing some of the information. For example, when two people are messaging each other it leaves encrypted codes from both sides and interpreted
to receive the message. When it is not encrypted it can allow people to find out what the messages are about and these can contain private information.
Unauthorized Access to Information
As people begin to adopt technology into their lives they do not consider the risks that come with it. In the modern world information is the most valuable
resource available to anyone which makes these resources sought out by people. These people are able to access people’s personal information by various means.
Such as ransomware, social engineering, and brute force attacks. When people try to download softwares, it could have a hidden malware within it which allows
the hackers to get control over the device. Some users are able to get into the network using the device and start accessing all the devices connected to it.
Ransomware is when the hackers hold the victim’s file as a hostage which they have encrypted for payment which could have a critical effect. This has a bigger
impact on major companies. For example, if a hacker were to hack a social media platform such as instagram and was able to get all the information of all the users.
It would leave the victims at risk of their personal information being leaked and the company would lose trust. Something that can be done to prevent this is to be
aware of the possibilities and have back ups of important files on a flash drive or device.

Another common way that hackers are able to access unauthorized information is through social engineering. This is when hackers manipulate individuals into revealing
confidential information through deception. An example of this is when someone impersonates as a tech support and they get them to send payment or passwords to accounts.
The older audience are the ones that are usually victims because they are unfamiliar with technology leaving them to depend on someone else for help. They are walking
blindly into these traps as they listen to anything that these hackers suggest because they would never suspect that these are impersonators. Some ways to prevent this
is by researching and asking around about the problem that they are searching, and if they are unable to find the information. They can ask a professional, but they should
make sure that it is a legitimate IT team. Then to spread the information to others to make sure that they will never be the victim.

Brute force is one of the most common ways to access unauthorized information. This is a process where the hackers try to get into accounts by using automated methods that
try to guess passwords by using many combinations continuously. This is highly effective on simple passwords such as the ones on old accounts or phones. This is dangerous
since once they get into the account they are able to have full control of it and start accessing information within it. There is also a possibility that they will change the
passwords and the information within it to prevent the users from reaccessing their accounts. Some ways to prevent brute force attacks is simply to use strong passwords that
have a longer length and mixes of characters which makes it much more difficult to crack. Also to use multi factor authentication which requires additional identification than
passwords which hackers will be unable to access which keeps the account safe even if they were able to find the right password. The most effective way to prevent this is to use
an account lockout mechanism which limits the number of attempts of password before the account locks. This makes the hacker use more time and resources to try and break in
which discourages them.
Benefits and Risks of Computing Innovations
Although technology has some disadvantages, there are much more benefits with it. It is important to know how to utilize these benefits and decrease the fear that people have
in technology since it can do a lot of good. The benefits of a computing innovation is the improved efficiency and productivity of work. Work such as AI is able to run tasks at
a faster rate and with minimum resources. These works would be free of human error and since it is constantly advancing to fix any errors it leaves behind. However a downside of
such technology is the possibility of job displacement since manual tasks can be now automated which would leave certain jobs unneeded. For example, fast food restaurants such
as McDonalds have established online orders and kiosks to replace the need for cashiers. These jobs would soon disappear leaving many with job displacement. However this does not
mean that it is an advancement of computing technology since it can create new job opportunities. This new field will be able to take in millions of people, however this will only
be appealing towards the new generation rather than the older generation. Since the new generation was raised while being surrounded by technology, this is much more familiar than
the older generation who have to learn everything in a different environment.

Another benefit of computing innovation are the convenient lifestyles that it brings. It allows people to be able to read any literature with a click or order food without having
to go in person. These are all very convenient, but it causes a lot of people to depend on technology to make it through their lives. With the popularity of AI it inspires people to
use it for anything such as generating ideas or doing a student’s homework. Also innovations such as auto driving which has been introduced to motor vehicles. These kinds of situations
question the idea of AI laws since it is hard to find a line of code at fault for something that they were programmed to do. For example if a car crashed due to an error or an Ai
suggesting disruptive solutions. Items such as alexa take in data constantly as they listen for the signal, but these data can be used harmfully. These can be sold to other companies for
marketing purposes, but these data can also be leaked to hackers who can now fully control what they hear within the vicinity of the device and obtain sensitive information.

Something that makes computing technology appealing is the change in the way that people are able to communicate and connect with each other. People are able to communicate in different
ways compared to the past since they are able to communicate over long distances such as halfway across the world with just a click of a button and be able to post anything that can reach
all audiences. This helps spread creativity and news very quickly and this is able to be accessed by anyone with social media which is what a lot of people have these days. However it comes
with risks such as the growth of cyberbullying. People are able to say what they want because they do not have the fear of being judged since they are hiding behind a screen. As well as the
social expectation of having access to technology which some people have problems with. This leaves people with lack of technology to fall behind with what is going on with the world since
businesses and schools are switching to digital methods. It produces unhealthy behaviors such as procrastination which leads to bad habits later on. However these innovations allow people to
access much more information at a faster rate.
Bibliography:
https://www.gao.gov/products/gao-22-106096
https://www.shrm.org/topics-tools/news/technology/people-data-collection-risks
https://www.womenslaw.org/about-abuse/ways-abusers-mis-use-technology/technology-tool-abuse/computer-crimes/what-are-some
https://www.okta.com/blog/2020/06/data-misuse/
https://www.syteca.com/en/blog/4-ways-detect-and-prevent-misuse-data
https://www.strongdm.com/blog/unauthorized-access
https://www.sailpoint.com/identity-library/unauthorized-access
https://www.uagrantham.edu/blog/technology-the-good-the-bad-the-ugly/
https://www.santanderopenacademy.com/en/blog/pros-and-cons-technology.html